Halfway There: How to Audit Your Business Tech Stack Before Q4 Hits
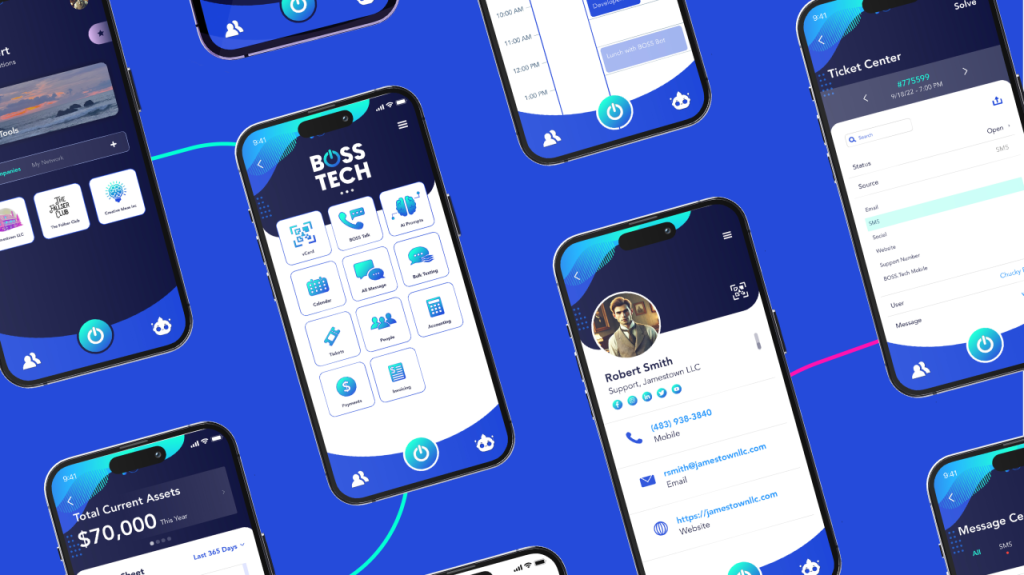
Halfway There: How to Audit Your Business Tech Stack Before Q4 Hits July marks the halfway point of the year — a prime time to pause and ask: Is your tech stack helping you scale, or is it quietly weighing you down? After months of using tools on autopilot, what kept you afloat in Q2 may not cut it in Q4. Now’s your chance to clean up, cut costs, and optimize. Why a Mid‑Year Tech Audit Matters App bloat and wasted spend are real: According to Productiv, around 53% of SaaS licenses go unused over a 90-day period—while companies average 371 apps in their portfolios. License waste hurts every business size: Zylo’s data show organizations typically waste over half of their SaaS licenses each month, costing a median of $21 million in unused software annually. Shadow IT keeps growing: Nearly 51% of apps are acquired outside of IT’s control—making your stack harder to manage. A tech audit helps you: Remove unused tools and subscriptions Reduce monthly operating costs Boost productivity through streamlined workflows Prevent tech debt from sneaking up come Q4 What to Review in Your Stack — A Practical Checklist Scheduling & Calendar Tools Do bookings, shifts, and meetings live on one calendar—or are you toggling across apps? Payment & Invoicing Is client billing seamless and mobile-friendly—or are you still chasing payments? Communication Platforms Is your team active in 2–3 apps—or lost across email, Slack, Teams, and WhatsApp? Client Data & CRM Are contact profiles accurate and accessible—or buried in spreadsheets and screenshots? Analytics & Reporting Are you getting timely insights—or only receiving data when someone digs out a report? Signs You’ve Outgrown Current Tools Look out for red flags such as: Needing 5+ tools to complete simple workflows New hires spending days just to learn your stack Important info shared only via screenshots or sticky notes A recurring subscription you rarely use If these sound familiar, it’s a signal your setup isn’t scaling with you. The Fix: Sync + Simplify with a SuperApp That’s exactly where BOSS.Tech steps in: All‑in‑one mobile SuperApp — manage calendar, payments, contacts, communications, and reports—all from your phone, from one SuperApp. AI People Sync — smart profile building and team syncing BOSS Bot automation — let repetitive tasks run on autopilot Custom-branded apps — set up your own platform with no coding required Think of it as your business’s command center—mobile-first, AI-enhanced, and tailored to your workflow. Audit Now, Scale Sooner Don’t wait for Q4 stress to hit before cleaning up. Block just 60 minutes this week to: List out your tools Mark what’s unused, redundant, or causing friction Plan what to retain—and where BOSS.Tech can consolidate When you’re ready to go from fragmented to frictionless, BOSS.Tech is here to simplify the rest. Ready to simplify your stack? Let’s do it together. Get Started Free Today or visit BOSS.Tech for more information!
Halfway There: How to Audit Your Business Tech Stack Before Q4 Hits Read More »